TABLE OF CONTENT
Introduction: The Shift from Breaking Systems to Breaking Trust
The modern enterprise no longer runs on a perimeter. It runs on pipelines.
Vulnerability scanners, Infrastructure-as-Code validators, AI gateways, and SDKs are embedded into development and deployment workflows, operating continuously with elevated privileges. These tools are not just part of the environment. They are trusted extensions of it.
The TeamPCP campaign in March 2026 demonstrates what happens when that trust is compromised. This was not an attack on infrastructure in the traditional sense. It was an attack on the systems that secure, validate, and deliver software itself. By poisoning this layer, TeamPCP gained privileged access to secrets, pipelines, and production environments, without ever needing to “break in.”
The Real Attack Surface: Security and Developer Infrastructure
At the center of this campaign is a strategic choice of targets. TeamPCP did not begin with applications or endpoints. It systematically compromised widely trusted tools embedded inside developer workflows, including:
- Trivy, a vulnerability scanner deeply integrated into CI pipelines
- KICS, an Infrastructure-as-Code security scanner
- LiteLLM, a widely used LLM proxy library
- The Telnyx Python SDK, extending reach into communications infrastructure
These tools share a critical characteristic. They operate inside trusted execution environments and inherit access to sensitive data by design. By compromising them, the attackers bypassed traditional security controls entirely. The malware executed as part of routine workflows, gaining immediate access to cloud credentials , CI/CD secrets, kubernetes configurations and SSH keys .
This is the core shift. The attack did not target weaknesses in code. It targeted trust in code execution paths.
Execution Model: How Malicious Code Moved Through Trusted Pipelines
The attack campaign leveraged software distribution channels themselves as the delivery mechanism. Malicious payloads were injected into:
- GitHub Actions workflows
- PyPI packages
- Container images and binaries
Once a developer pipeline invoked one of these components, the malware executed automatically within a trusted context. No additional exploit was required. The delivery techniques evolved rapidly over the course of the campaign, refelcting a deliberate attempt to balance stealth, reliability, and cross-platform execution.
- Initial payloads used inline Base64 encoding
- This shifted to .pth auto-execution, enabling code to run implicitly during Python initialization
- The campaign then moved to split-file WAV steganography, embedding payloads within benign-looking audio files
- Execution expanded from Linux environments to include Windows persistence
What Was Stolen: Not Data, but Access
The objective of the campaign was not traditional data exfiltration. It was the systematic harvesting of credentials that enable control. Across compromised environments, the malware extracted:
- AWS access keys
- Azure application secrets
- SaaS tokens
- Kubernetes configuration files
- SSH keys
- CI/CD pipeline secrets
These represent control points and what the attackers were effectively collecting can be described as a map of the organization’s operational infrastructure.
Speed of Exploitation: Hours, Not Days
What distinguishes this campaign is how quickly the attackers moved after gaining access.
Secret validation was nearly instant. Within hours of the initial compromise, stolen credentials were verified using TruffleHog, an open-source tool that validates secrets by making live API calls to their respective providers. AWS access keys were confirmed active via sts:GetCallerIdentity. Azure application secrets and SaaS tokens were similarly checked.
By the time most organizations became aware of the compromise, their credentials had already been confirmed active and queued for use. This compresses the traditional detection window to near zero.
From Access to Control: Post-Compromise Operations
Once credentials were validated, the attackers transitioned immediately into structured exploitation.
Reconnaissance began within 24 hours. Across AWS environments, TeamPCP enumerated IAM users and roles, EC2 instances, Lambda functions, RDS databases, S3 buckets, and Route 53 hosted zones. There was a clear emphasis on containerized environments. ECS clusters and task definitions were mapped in detail, identifying targets for direct execution. AWS Secrets Manager was catalogued for bulk extraction.
Lateral movement followed predictable but highly effective paths. GitHub Personal Access Tokens were used to create pull requests containing malicious workflows, allowing execution inside targeted repositories. In parallel, ECS Exec enabled command execution directly within live containers.
Notably, these actions relied entirely on legitimate tools and APIs. There were no exploits in the traditional sense. The attacker behavior resembled a developer operating at scale.
Exfiltration at Scale: Aggressive, Not Silent
Data exfiltration was not cautious. It was industrial. Private repositories were cloned at scale using git.clone. Data was extracted in bulk from S3 buckets, Secrets Manager, and databases. Naming conventions such as “pawn” and “massive-exfil” suggest that stealth was not the priority.
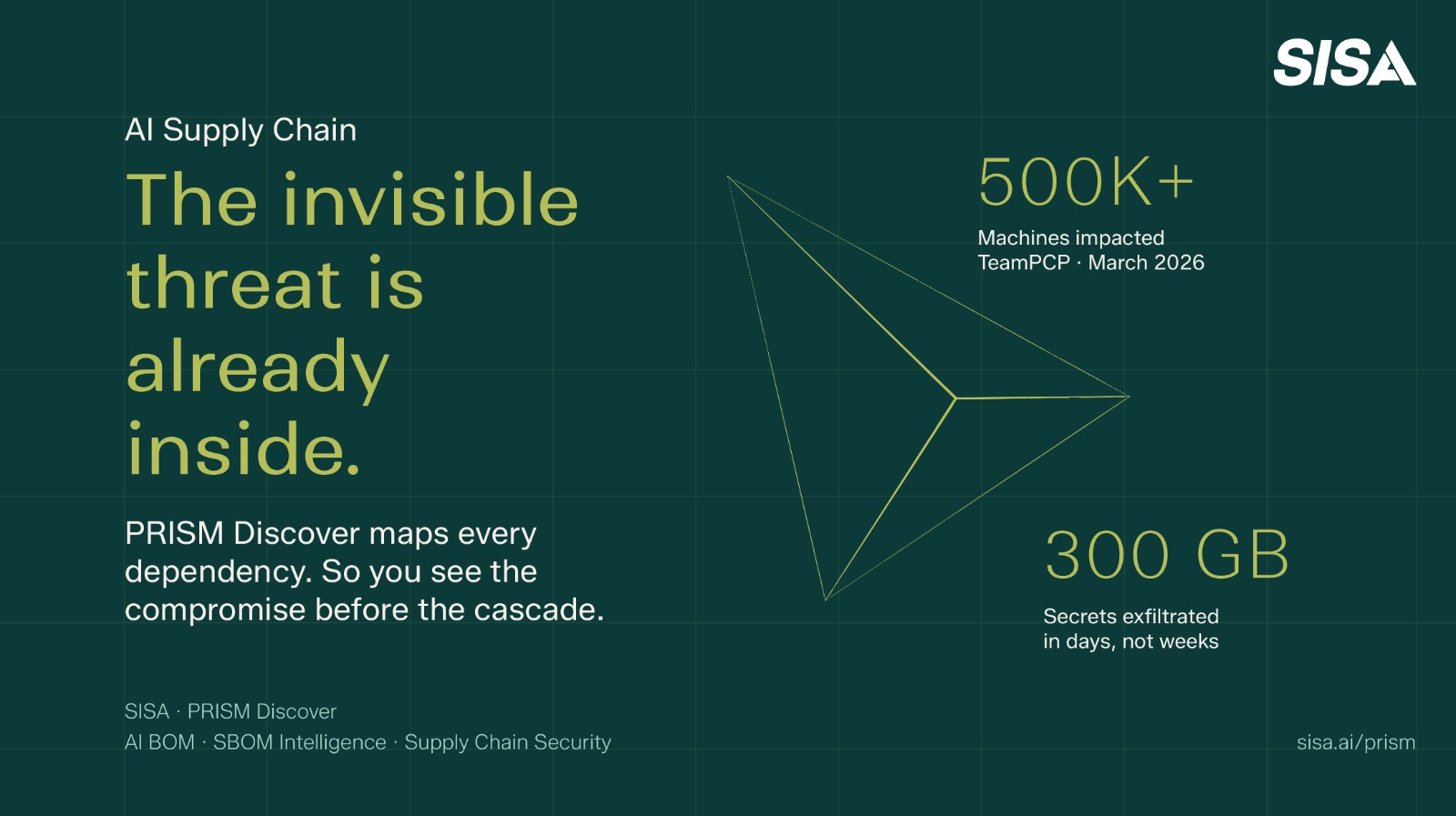
Estimates indicate that over 500,000 machines impacted and More than 300 GB of data and secrets exfiltrated
Beyond initial compromise, stolen tokens were used to infect additional packages, extending the campaign’s reach further into downstream ecosystems.
The Cascade Effect: How One Compromise Becomes Many
The most important aspect of this campaign is how the compromises connected.
The attack began with a retained credential from a prior Trivy compromise. From there, it expanded across multiple tools and ecosystems, including GitHub Actions, PyPI, Docker Hub, and OpenVSX.
Critically, not every affected organization directly used all compromised tools. For example, LiteLLM was impacted because its build pipeline depended on Trivy. This is the essence of the problem.
Transitive dependencies create invisible attack paths
Traditional third-party risk management does not account for these relationships because there is no direct vendor engagement to assess. Yet these dependencies sit inside production pipelines with full access to sensitive environments.
What TeamPCP demonstrated is that a single compromised component can act as the starting point for a cascading chain of compromise across ecosystems.
Why This Attack Model Works
Several structural realities make this type of attack particularly effective.
Security tooling is inherently trusted and often runs with elevated permissions. Compromising a vulnerability scanner or CI/CD component provides immediate access to sensitive systems.
CI/CD pipelines have become one of the most privileged identities in the enterprise. They aggregate credentials for deployment, infrastructure management, and repository access.
Speed favors the attacker. The interval between compromise and exploitation is now measured in hours, rendering traditional detection approaches too slow.
Finally, attackers are leveraging legitimate tools and workflows. There are no obvious anomalies at the technical level. The attacker looks like a valid user performing valid actions, just at an unusual scale and velocity.
What This Means for the Evolution of the Supply Chain
The TeamPCP campaign marks a clear inflection point in how sophisticated attackers are approaching the supply chain. This was not an attack on model behavior, prompt injection, or an application flaw. It was a true software supply chain compromise. Malicious packages were introduced into trusted ecosystems, credentials were harvested at scale, and persistence was established inside environments that believed they were secure by design.
What makes this fundamentally more consequential than earlier AI-related attacks is the blast radius. The risk is no longer confined to a single model, application, or endpoint. It extends into the development and release pipeline itself, where trust is assumed, privileges are aggregated, and execution is automated.
In this model, attackers do not need to break systems, they position themselves inside the systems that build and secure them.
That changes the nature of defense. Security can no longer rely on protecting perimeters or validating individual components in isolation. It must evolve toward continuous visibility, dependency intelligence, and pipeline-aware controls.
Because in the next generation of supply chain attacks, the question is not whether a component is vulnerable but whether you even know it exists.
The Policy Signal: Visibility Is Now a Requirement, Not a Choice
The technical reality exposed by TeamPCP is now being formally recognized at a policy level. On 18 March 2026, the National Security Agency (NSA) issued guidance explicitly identifying AI Bills of Materials (AI BOMs) as a required control for managing AI supply chain risk.
This is a critical shift. It reframes the problem from detection to visibility as a foundational control. Organisations are no longer being asked to secure what they deploy. They are being asked to first know, with precision, what they are running across increasingly complex AI and software ecosystems.
Introducing SISA PRISM: Making the Invisible Visible
SISA PRISM is built around this exact problem. Within PRISM, PrismDiscover functions as the AI BOM and SBOM intelligence layer. Its role is straightforward but foundational:
- Continuously map every AI component, package, and dependency across the environment
- Maintain an up-to-date inventory of what is actually in use
- Flag exposure when a known vulnerability or compromised package is identified
PrismDiscover runs on structured, recurring scan cycles that maintain consistent visibility across dynamic AI and software environments. When a vulnerable or compromised component is detected, it is highlighted in the subsequent scan cycle, enabling prompt evaluation, prioritized remediation, and action before exposure expands across pipelines and production systems.
For CISOs, this means measurable oversight, disciplined response, and governance clarity over dependencies that typically operate beyond direct visibility.
The next generation of supply chain risk will not announce itself, it will move through what you already trust. Strengthen your visibility with PrismDiscover.